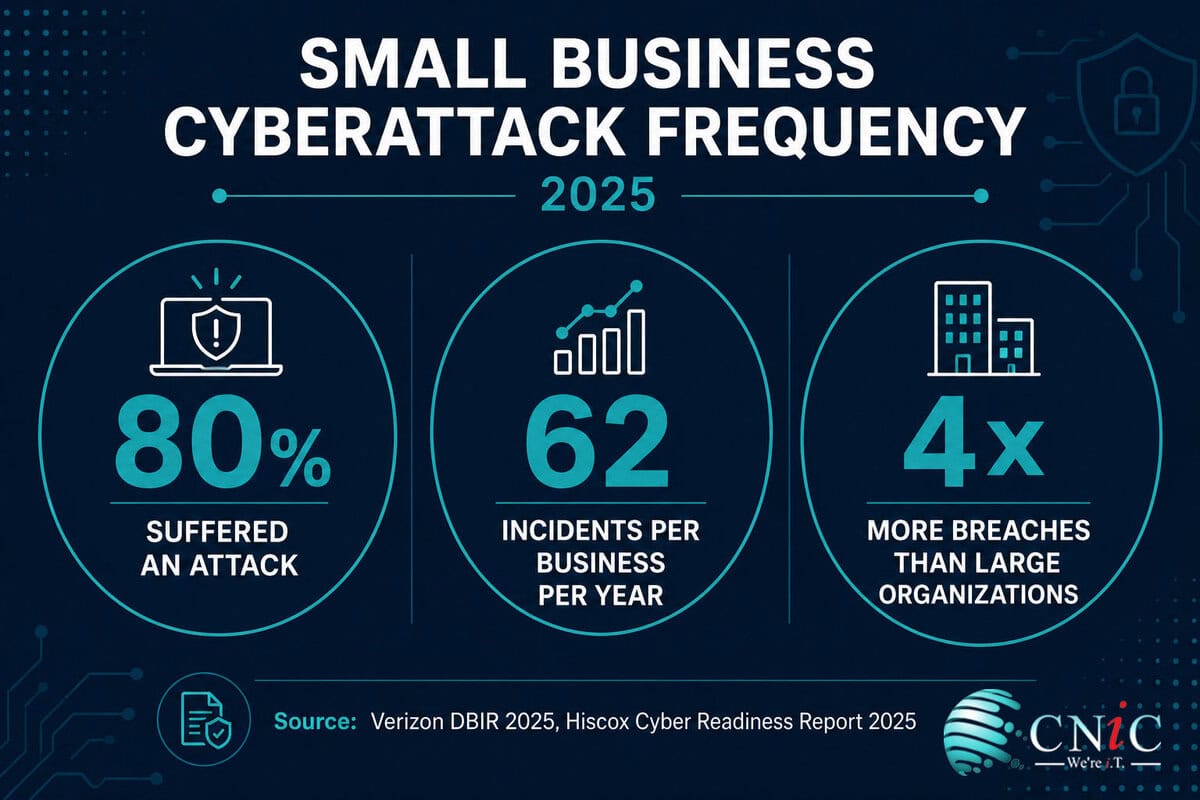
Small and medium businesses experienced approximately 4 times more confirmed data breaches than large organizations in 2025 — and 80% of small businesses suffered at least one cyberattack during the year. The idea that small businesses are too small to target is not just wrong. It is the attack vector (Verizon 2025 DBIR; Hiscox Cyber Readiness Report 2025).
Attackers do not avoid small businesses because of their size. They seek them out because of it. Limited IT budgets, lean security teams, and a persistent belief that “we’re too small to matter” have turned SMBs into the most reliably exploitable target category in the threat landscape. Ransomware-as-a-Service has industrialized the economics: criminal groups rent sophisticated infrastructure, automation handles scale, and SMBs pay the price.
We aggregated data from the Verizon 2025 Data Breach Investigations Report, IBM Cost of a Data Breach Report 2025, Hiscox Cyber Readiness Report 2025 (5,750 SMEs, 8 countries), FBI Internet Crime Complaint Center 2025 Annual Report, VikingCloud 2025 SMB Security Survey, StrongDM 2025, and the US Chamber of Commerce. 50 verified data points. Every stat traced to a primary source. Updated May 2026.
Key Takeaways
- SMBs experienced approximately 4× more confirmed breaches than large organizations in 2025 (Verizon DBIR, 2025).
- 80% of small businesses suffered at least one cyberattack in 2025 — and 41% of those incidents were AI-driven (StrongDM / Verizon, 2025).
- 59% of SMEs globally reported experiencing a cyberattack in the past 12 months (Hiscox Cyber Readiness Report, 2025).
- 88% of SMB breaches involved ransomware — compared to just 39% for large organizations (Verizon DBIR, 2025).
- Small businesses receive targeted malicious emails at 1 in every 323 emails — the highest rate of any organization size (Verizon DBIR, 2025).
- Employees at small businesses experience 350% more social engineering attacks than employees at large enterprises (StrongDM / Verizon DBIR).
- The average SMB breach costs $3.31 million for organizations under 500 employees — with a realistic incident range of $120,000–$1.24 million (IBM 2025; Verizon DBIR 2025).
- Downtime from a cyberattack costs $53,000 per hour (VikingCloud Research, 2025).
- 40% of SMBs say a cyberattack costing $100,000 or less would put them out of business (VikingCloud, 2025).
- 47% of businesses with fewer than 50 employees allocate zero cybersecurity budget (StrongDM, 2025).
- Only 17% of US small businesses have cyber insurance despite being prime targets (StrongDM, 2025).
- 69% of US companies reported an increase in cyberattacks compared to the previous year (Hiscox Cyber Readiness Report, 2025).
1 How Often Small Businesses Are Attacked
The frequency data from 2025 removes any remaining ambiguity: small businesses are not occasional collateral damage in attacks aimed at enterprises. They are primary targets. The Verizon DBIR 2025 recorded 3,049 SMB security incidents with 2,842 confirmed breaches — a record. Hiscox’s 2025 Cyber Readiness Report, which surveyed 5,750 SMEs across 8 countries, found 59% reported an attack in the past 12 months, with US companies averaging 62 cyber incidents per business per year — more than one per week. The misconception that small businesses are safe because of their size is not just wrong — it is functionally dangerous. Among SMB owners with no security measures in place, 59% still believe they are too small to be attacked.
| Metric | Value | Source |
|---|---|---|
| SMB confirmed breaches (2025 Verizon dataset) | 2,842 confirmed breaches from 3,049 incidents | Verizon DBIR, 2025 |
| SMB breach rate vs. large organizations | ~4× more confirmed breaches | Verizon DBIR, 2025 |
| Small businesses suffering at least one attack (2025) | 80% | StrongDM / Verizon, 2025 |
| SMEs experiencing attack in past 12 months (global) | 59% | Hiscox Cyber Readiness Report, 2025 |
| US companies reporting increased attack frequency YoY | 69% | Hiscox Cyber Readiness Report, 2025 |
| Average cyber incidents per US business per year | 62 incidents (~1.2 per week) | Hiscox Cyber Readiness Report, 2025 |
| SMB owners with no security who believe they’re too small to target | 59% | StrongDM, 2025 |
| AI-driven incidents among SMB attacks | 41% of all SMB incidents | StrongDM / Verizon, 2025 |
Verizon 2025 DBIR → | Hiscox Cyber Readiness Report 2025 →
Get a Free SMB Cybersecurity Assessment From CNiC →
2 The Real Cost of a Cyberattack on a Small Business
The IBM average of $3.31 million per SMB breach is real but abstract for a business with 10 employees. The Verizon DBIR 2025 range of $120,000 to $1.24 million is more representative of what typical SMB incidents actually cost. But even $120,000 represents an existential shock for most small businesses — particularly when you factor in that downtime costs $53,000 per hour, breach costs have a long tail (47% land in year one, 29% in year two, 24% persist beyond two years), and only 17% of US small businesses carry cyber insurance. The math is unambiguous: prevention costs 50–60 times less than recovery.
| Cost Metric | Value | Source |
|---|---|---|
| Average SMB data breach cost (under 500 employees) | $3.31 million | IBM Cost of Data Breach, 2025 |
| Realistic SMB incident cost range | $120,000–$1.24 million | Verizon DBIR, 2025 |
| Downtime cost per hour | $53,000/hour | VikingCloud Research, 2025 |
| SMBs saying a $100K attack would end their business | 40% | VikingCloud, 2025 |
| SMBs saying ransomware would end their business | 75–78% | ConnectWise / VikingCloud, 2025 |
| Annual prevention cost (typical SMB) | $5,000–$15,000 | AlphaCIS, 2026 |
| Prevention vs. recovery cost ratio | 50–60× cheaper to prevent | AlphaCIS, 2026 |
| Breach costs persisting beyond year one | 53% of total cost lands in years 2+ | IBM Cost of Data Breach, 2023/2025 |
| SMBs facing bankruptcy post-attack | 19% | Verizon DBIR, 2025 |
| Post-breach business impact: reduction in performance indicators | 30% of attacked SMEs | Hiscox Cyber Readiness Report, 2025 |
Verizon 2025 DBIR → | IBM Cost of Data Breach 2025 →
3 How Small Businesses Get Attacked: Top Vectors
Phishing is the entry point of choice for attackers targeting small businesses — not because it is the most sophisticated method, but because it is the most reliable. Small businesses receive targeted malicious email at a rate of 1 in every 323 emails, the highest of any organization size category. Their employees experience 350% more social engineering attacks than employees at large enterprises. 72% of workers say phishing attempts are more convincing than a year ago because of AI-generated language — and small businesses are the least likely to have security awareness training in place to compensate.
Top cyberattack vectors targeting small businesses (2025)
Source: Hiscox Cyber Readiness Report 2025; Verizon DBIR 2025. Phishing and ransomware cited as top SMB challenges (Hiscox 2025).
| Attack Vector | SMB Stat | Source |
|---|---|---|
| Phishing as top SMB threat | 47% cite phishing as biggest challenge; 1 in 323 emails is targeted | Hiscox 2025; Verizon DBIR 2025 |
| Ransomware presence in SMB breaches | 88% of SMB breaches involved ransomware | Verizon DBIR, 2025 |
| Social engineering attack rate vs. large orgs | 350% more attacks at businesses under 100 employees | StrongDM / Verizon DBIR |
| AI-generated phishing convincingness | 72% of workers say phishing more convincing due to AI | Sagiss / Pollfish Survey, Feb 2026 |
| Business email compromise (BEC) losses | $3 billion in US losses; median BEC loss ~$50,000 for SMBs | FBI IC3, 2025 |
| Third-party / supply chain breach involvement | 30% of breaches (doubled YoY) | Verizon DBIR, 2025 |
| External actors responsible for SMB breaches | 91% — primarily financially motivated | Verizon DBIR, 2025 |
| Workers clicking suspicious links in past year | 63% later felt they should have double-checked | Sagiss / Pollfish Survey, Feb 2026 |
Hiscox Cyber Readiness Report 2025 →
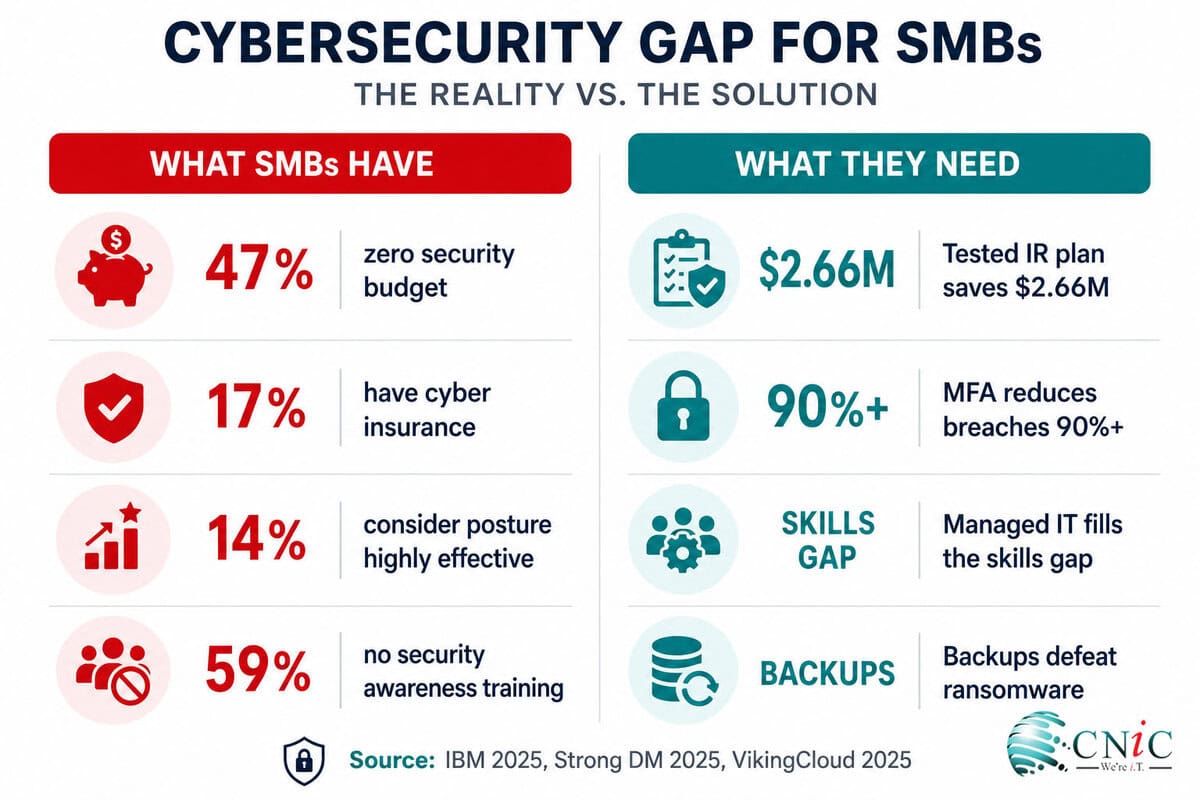
4 SMB Cybersecurity Preparedness: The Gap
The preparedness data is the most sobering part of the SMB cybersecurity picture. Not because attacks are inevitable — many are preventable — but because the most effective defenses are also the most consistently absent. 47% of businesses with fewer than 50 employees allocate zero cybersecurity budget. Only 14% of small businesses consider their cybersecurity posture highly effective. 83% say they are not financially prepared to recover from a cyberattack. The gap between perceived risk and actual investment creates exactly the conditions attackers rely on.
| Preparedness Metric | Value | Source |
|---|---|---|
| SMBs with zero cybersecurity budget (under 50 employees) | 47% | StrongDM, 2025 |
| Small businesses with no formal cybersecurity plan | More than 50% | US Chamber of Commerce / 2025 surveys |
| SMBs with no incident response plan | 66% | IBM / Guardz, 2025 |
| Small businesses with cyber insurance | Only 17% (US) | StrongDM, 2025 |
| SMBs using AI-powered security tools | Only 11% | CrowdStrike SMB Security Survey, 2025 |
| SMBs considering cybersecurity posture highly effective | Only 14% | NinjaOne / Cybersecurity Magazine, 2025 |
| SMBs not financially prepared to recover from attack | 83% | NinjaOne / Cybersecurity Magazine, 2025 |
| SMBs without security awareness training | 59% | Hiscox Cyber Readiness Report, 2025 |
| SMBs without network-based firewalls | 43% | Hiscox Cyber Readiness Report, 2025 |
| SMBs planning to increase cybersecurity spending next year | 94% | Hiscox Cyber Readiness Report, 2025 |
Hiscox Cyber Readiness Report 2025 → | StrongDM SMB Cybersecurity Statistics →
Build a Security Strategy With CNiC’s Virtual CIO →
5 The Human Factor: Employees as the Frontline
95% of cybersecurity incidents at SMBs involve human error as a contributing factor. This is not a failure of character — it is a failure of preparation. Employees at small businesses are bombarded with social engineering attacks at 3.5 times the rate of their enterprise counterparts, without the benefit of the security awareness programs that enterprise employees receive. The math strongly favors investment in training: quarterly phishing simulations cost a fraction of a single incident and consistently deliver the highest measurable ROI of any security control available to SMBs.
| Human Factor Metric | Value | Source |
|---|---|---|
| Cybersecurity incidents involving human error | 95% | NinjaOne / Cybersecurity Magazine, 2025 |
| Human element involved in all breaches (all sizes) | 60% | Verizon DBIR, 2025 |
| SMBs without security awareness training | 59% | Hiscox Cyber Readiness Report, 2025 |
| Workers who clicked a suspicious link in past year | 63% | Sagiss / Pollfish Survey, Feb 2026 |
| Workers saying phishing more convincing due to AI | 72% | Sagiss / Pollfish Survey, Feb 2026 |
| SMB employees experiencing social engineering vs. enterprise | 350% more attacks | StrongDM / Verizon DBIR |
| SMBs where employees struggle with burnout post-breach | 32% | Hiscox Cyber Readiness Report, 2025 |
| Customer attrition risk post-breach | 55% of consumers less likely to do business with breached company | StrongDM, 2025 |
6 What Actually Works: SMB Defense Statistics
The good news in the 2025 SMB data is that the most effective defenses are also the most accessible. Multi-factor authentication reduces successful attacks by 90% and costs almost nothing to implement. A tested incident response plan saves $2.66 million per breach (IBM 2025) and costs nothing to create. A 3-2-1 backup strategy costs under $500 per year and eliminates ransomware extortion leverage entirely. The gap is not capability — it is awareness and implementation. Organizations that implement even three of the top five controls consistently recover faster and at significantly lower cost.
| Defense Control | Impact | Source |
|---|---|---|
| Multi-factor authentication (MFA) | 90% reduction in successful attacks | Total Assure Research, 2025 |
| Tested incident response plan | $2.66 million saved per breach | IBM Cost of Data Breach, 2025 |
| AI/automation in security operations | $1.9 million saved per breach; 80-day faster detection | IBM Cost of Data Breach, 2025 |
| Zero trust architecture | $1.76 million saved per breach | IBM Cost of Data Breach, 2025 |
| 3-2-1 backup strategy | Eliminates ransomware extortion leverage; under $500/year | AlphaCIS, 2026 |
| Security awareness training (quarterly) | Highest ROI of any security measure; reduces click rate significantly | IBM / KnowBe4, 2025 |
| Managed IT services | Reduces detection time; fills skills gap; closes monitoring gaps | Various MSP benchmarks, 2025 |
| Law enforcement engagement | $990,000 saved per breach; sometimes provides decryption keys | IBM Cost of Data Breach, 2025 |
IBM Cost of Data Breach 2025 →
Small Business Cybersecurity by the Numbers: Summary
| Metric | Value | Source |
|---|---|---|
| SMB breach rate vs. large organizations | ~4× more | Verizon DBIR, 2025 |
| SMB confirmed breaches (2025) | 2,842 | Verizon DBIR, 2025 |
| Small businesses attacked in 2025 | 80% | StrongDM / Verizon, 2025 |
| SMEs experiencing attack globally (past 12 months) | 59% | Hiscox, 2025 |
| Ransomware in SMB breaches | 88% | Verizon DBIR, 2025 |
| Ransomware in large-org breaches | 39% | Verizon DBIR, 2025 |
| Targeted malicious email rate (SMBs) | 1 in 323 emails | Verizon DBIR, 2025 |
| Social engineering attacks vs. large orgs | 350% more | StrongDM / Verizon DBIR |
| Average SMB breach cost (under 500 employees) | $3.31 million | IBM, 2025 |
| Realistic SMB incident range | $120K–$1.24M | Verizon DBIR, 2025 |
| Downtime cost per hour | $53,000/hour | VikingCloud, 2025 |
| SMBs saying $100K attack ends business | 40% | VikingCloud, 2025 |
| SMBs facing bankruptcy post-attack | 19% | Verizon DBIR, 2025 |
| SMBs with zero cybersecurity budget | 47% (under 50 employees) | StrongDM, 2025 |
| SMBs with no incident response plan | 66% | IBM / Guardz, 2025 |
| SMBs with cyber insurance | Only 17% | StrongDM, 2025 |
| Human error in SMB incidents | 95% | NinjaOne / Cybersecurity Magazine, 2025 |
| MFA attack reduction rate | 90% | Total Assure Research, 2025 |
| IR plan savings per breach | $2.66 million | IBM, 2025 |
| Prevention vs. recovery cost ratio | 50–60× cheaper | AlphaCIS, 2026 |
Frequently Asked Questions
What percentage of cyberattacks target small businesses?
43% of all cyberattacks target small businesses according to widely cited industry data. More recently, the Verizon 2025 DBIR confirmed SMBs experienced approximately 4 times more confirmed breaches than large organizations, recording 2,842 confirmed breaches in 2025 alone. 80% of small businesses suffered at least one cyberattack during 2025, and 59% of SMEs globally reported an attack in the past 12 months (Hiscox Cyber Readiness Report 2025).
How much does a cyberattack cost a small business?
Costs vary widely. IBM’s Cost of a Data Breach Report puts the average SMB breach cost (under 500 employees) at $3.31 million. Verizon’s 2025 DBIR puts the realistic range for most SMB incidents at $120,000 to $1.24 million. Downtime costs $53,000 per hour (VikingCloud 2025). 40% of SMBs say a cyberattack costing $100,000 or less would put them out of business — and 19% of attacked SMBs face bankruptcy (Verizon DBIR 2025).
What is the most common cyberattack on small businesses?
Phishing is the #1 attack vector for small businesses, with 1 in every 323 emails at small businesses being a targeted malicious email — the highest rate of any organization size. Ransomware was present in 88% of SMB breaches in 2025. Employees at small businesses experience 350% more social engineering attacks than employees at large enterprises (StrongDM / Verizon DBIR 2025).
Why are small businesses targeted by hackers?
Small businesses hold valuable data but typically lack enterprise-grade defenses. 59% of SMB owners with no security believe they are too small to be attacked — that misconception is itself an attack vector. Ransomware-as-a-Service has industrialized attacks, making it economically viable to target small organizations at scale. Micro-businesses experience a 43% breach success rate on attempted attacks, compared to 18% for mid-sized organizations (Total Assure Research 2025).
Do small businesses need cybersecurity insurance?
Yes — but most don’t have it. Only 17% of US small businesses have cyber insurance despite being prime targets (StrongDM 2025). The cyber insurance market is growing from $8.5 billion in 2021 to a projected $34 billion by 2031, and insurers are increasingly requiring proof of MFA, endpoint protection, and regular vulnerability assessments before issuing policies. Given that 40% of SMBs say a $100K attack would end their business, cyber insurance is no longer optional.
Methodology & Sources
All statistics traced to primary or verified Tier 2 sources. Where commonly cited figures have been officially debunked (including the “60% closure” stat), we note this explicitly and provide verified alternatives.
Primary sources used
- Verizon 2025 Data Breach Investigations Report (DBIR) — 22,000+ incidents, 12,195 confirmed breaches, SMB subset. verizon.com →
- Hiscox Cyber Readiness Report 2025 — 5,750 SMEs, 8 countries, Wakefield Research. hiscoxgroup.com →
- IBM Cost of a Data Breach Report 2025 — 600 organizations, Ponemon Institute. ibm.com →
- FBI Internet Crime Complaint Center (IC3) 2025 Annual Report. fbi.gov →
- VikingCloud SMB Security Research 2025 — downtime costs, financial impact data.
- StrongDM 2025 SMB Cybersecurity Statistics — budget, insurance, preparedness data. strongdm.com →
- Sagiss / Pollfish SMB Phishing Survey — 500 US desk workers, February 2026.
- AlphaCIS 2026 — prevention vs. recovery cost analysis.
- Total Assure Research 2025 — MFA effectiveness, attack success rates by business size.
Last updated: May 2026. Update schedule: Updated quarterly as primary reports are released.
Myth correction: The “60% of small businesses close within 6 months of a cyberattack” statistic was officially disavowed by the National Cyber Security Alliance (NCSA) in 2022. We do not use it. The Verizon DBIR 2025 figure of 19% facing bankruptcy is the most reliable current alternative.
related posts
Ransomware Payout Statistics 2026: What Victims Actually Pay
May 15, 2026Ransomware payments tell a story of contradictions. In 2024, total global ransom payments dropped 35% year-over-year…
Average Cost of a Data Breach Statistics (2026): By Industry, Country &…
May 14, 2026The average data breach now costs US organizations $10.22 million — an all-time high for any…
Ransomware Statistics (2026): Attacks, Costs & Industry Targets
May 14, 2026Ransomware was present in 44% of all confirmed data breaches in 2025 — up from 32%…
Cybersecurity Statistics (2026): 52+ Data Points on Cybercrime
May 14, 2026US cybercrime losses hit $20.9 billion in 2025 — a 26% jump year-over-year and the first…