Ransomware was present in 44% of all confirmed data breaches in 2025 — up from 32% the prior year — making it the single most dominant threat pattern in the Verizon Data Breach Investigations Report’s 20-year history.
At the same time, organizations are fighting back. The median ransom payment fell to $115,000 in 2025, the percentage of victims refusing to pay climbed to 64%, and average recovery times dropped by nearly half. The story of ransomware in 2026 is one of escalating attack volume meeting improving defenses — but with small and medium businesses still dangerously exposed.
We aggregated data from the Verizon 2025 Data Breach Investigations Report, Sophos State of Ransomware 2025 (3,400 organizations surveyed), IBM Cost of a Data Breach Report 2025, FBI Internet Crime Complaint Center 2025 Annual Report, Check Point Cyber Security Report 2026, and HIPAA Journal ransomware tracking. Every stat is traced to its primary source. 48 verified data points. Updated May 2026.
Key Takeaways
- Ransomware was present in 44% of all confirmed breaches in 2025, up from 32% — a 37% year-over-year increase (Verizon DBIR, 2025).
- 88% of SMB breaches involved ransomware, compared to just 39% for large organizations — a 2.3× gap (Verizon DBIR, 2025).
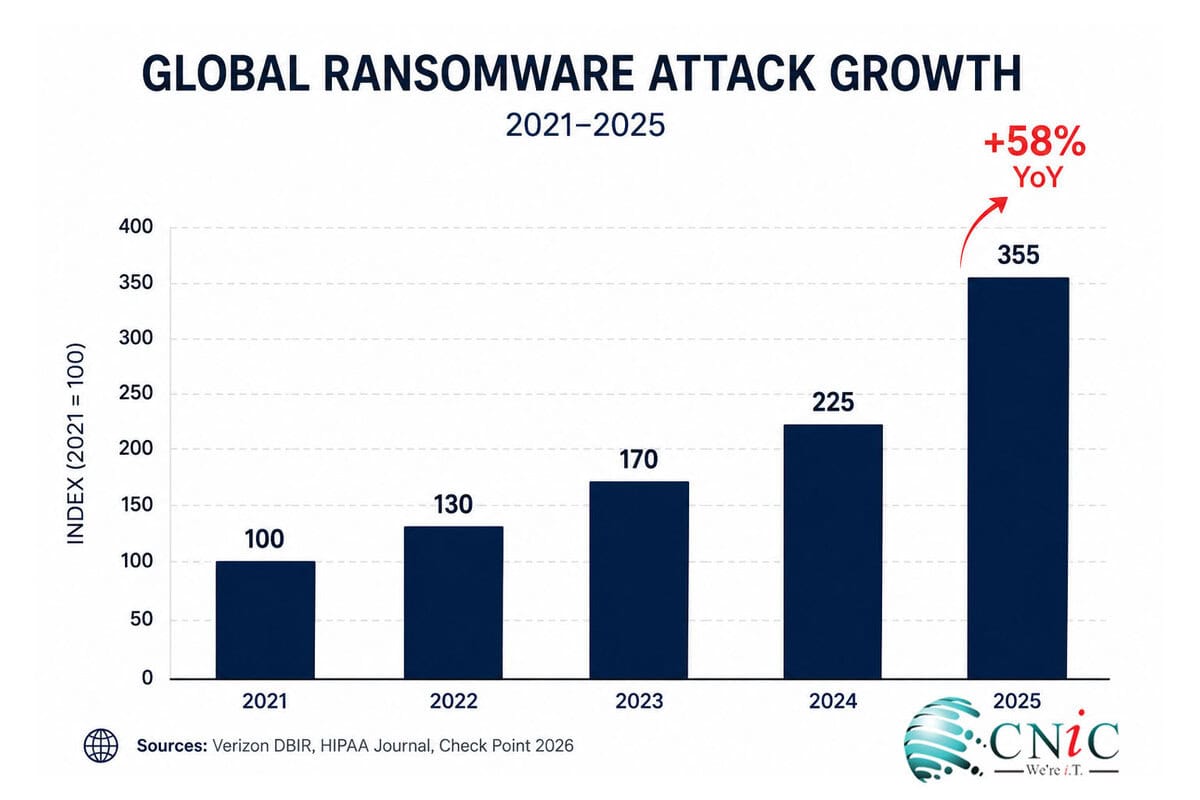
- Global ransomware attacks increased 58% in 2025 year-over-year, with 55% of attacks targeting US-based organizations (HIPAA Journal / GRIT, 2025).
- The median ransom payment fell to $115,000 in 2025 (Verizon DBIR), while Sophos reports the mean payment was $1 million — down 50% from $2 million in 2024 (Sophos State of Ransomware, 2025).
- 64% of ransomware victims refused to pay in 2025, up from 50% two years prior (Verizon DBIR, 2025).
- Average recovery cost excluding ransom fell 44% to $1.53 million in 2025, down from $2.73 million in 2024 (Sophos State of Ransomware, 2025).
- The average total cost of a ransomware incident including downtime and remediation is $5.08 million (IBM Cost of Data Breach, 2025).
- 53% of organizations fully recovered within one week in 2025, up from 35% in 2024 (Sophos, 2025).
- Exploited vulnerabilities are the most common ransomware entry point at 32% of attacks, followed by compromised credentials (23%) and phishing (18%) (Sophos, 2025).
- Manufacturing is the most targeted sector by volume; healthcare remains the most expensive at $7.42 million average breach cost (IBM, 2025).
- 85% of ransomware attacks go unreported to law enforcement (BlackFog, 2025).
- An estimated 84% of organizations that paid ransom failed to fully recover all their data (Halcyon Research, Q4 2024).
1 Ransomware Attack Volume & Frequency
The raw numbers are stark: ransomware attacks increased 58% globally in 2025, with an estimated attack occurring somewhere in the world every 19 seconds. Ransomware-as-a-Service (RaaS) has industrialized the attack model — criminal groups now operate as franchises, recruiting affiliates, sharing infrastructure, and providing negotiation support. Law enforcement takedowns of major groups like LockBit and RansomHub did not reduce overall attack volume — they fragmented the ecosystem and accelerated affiliate migration to surviving platforms.
| Metric | Value | Source |
|---|---|---|
| Global ransomware attack increase (2025 vs. 2024) | 58% year-over-year | HIPAA Journal / GRIT, 2025 |
| Ransomware present in all confirmed breaches | 44% (up from 32%) | Verizon DBIR, 2025 |
| Estimated global attack frequency | Every ~19 seconds | Total Assure Research, 2025 |
| Share of attacks targeting US organizations | 55% | HIPAA Journal / GRIT, 2025 |
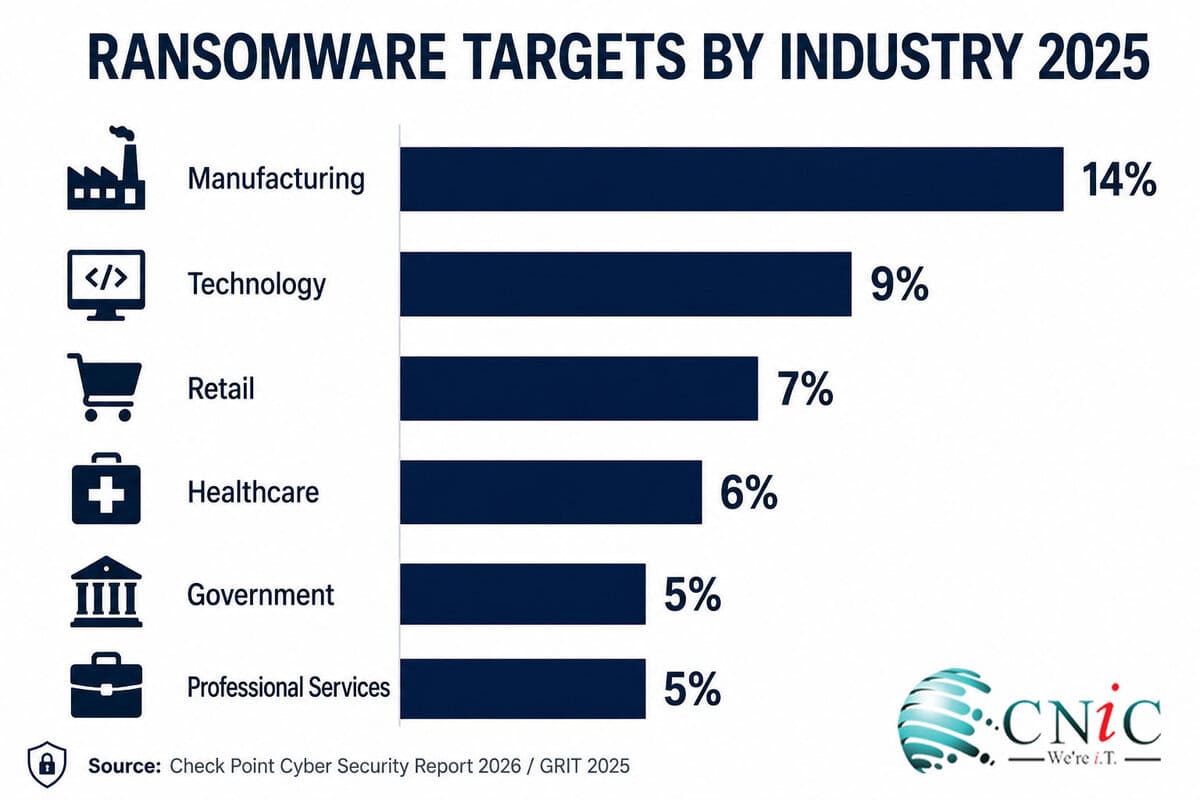
| Most targeted sector by volume | Manufacturing (14% of attacks) | Check Point / GRIT, 2025 |
| Ransomware attacks not reported to law enforcement | ~85% | BlackFog Ransomware Report, 2025 |
| Ransomware incidents increase over prior 5 years | More than doubled | Verizon DBIR, 2025 |
Verizon 2025 DBIR → | HIPAA Journal Ransomware Report →
2 Ransom Payments & Total Incident Costs
The economics of ransomware are shifting in favor of defenders — but not uniformly. The Verizon-tracked median payment fell to $115,000, while Sophos (surveying organizations that actually experienced attacks) found the mean payment was $1 million. Both are legitimate figures for different questions. What is consistent across all sources: total recovery costs vastly exceed the ransom itself — downtime, forensics, legal fees, and reputational damage routinely multiply the ransom amount by 5 to 10 times.
Median ransomware payment by sector (Sophos State of Ransomware 2025)
Healthcare pays the lowest median despite the highest breach cost — reflecting both higher refusal rates and negotiation outcomes. Source: Sophos 2025, Comparitech
| Metric | Value | Source |
|---|---|---|
| Median ransomware payment (broad dataset) | $115,000 (down from $150K) | Verizon DBIR, 2025 |
| Mean ransomware payment (organizations surveyed) | $1 million (down 50% from $2M in 2024) | Sophos State of Ransomware, 2025 |
| Median ransom demand | $1.32 million | Sophos State of Ransomware, 2025 |
| Organizations that paid less than the demand | 53% (via negotiation) | Sophos State of Ransomware, 2025 |
| Average total ransomware incident cost | $5.08 million | IBM Cost of Data Breach, 2025 |
| Average recovery cost excluding ransom (global) | $1.53 million (down 44% from $2.73M) | Sophos State of Ransomware, 2025 |
| Recovery cost for SMBs (100–250 employees) | $638,536 excluding ransom | Sophos State of Ransomware, 2025 |
| Highest median payment by sector | $2.5 million — state & local government | Sophos State of Ransomware, 2025 |
Sophos State of Ransomware 2025 → | IBM Cost of Data Breach 2025 →
⚠ Should you pay? The data argues strongly against it. 84% of organizations that paid in Q4 2024 failed to fully recover all their data (Halcyon Research). Paying funds future attacks and may violate OFAC sanctions if the group is sanctioned. The FBI can sometimes provide decryption keys when incidents are reported promptly.
3 Ransomware Attack Vectors & Entry Points
Ransomware is almost never the initial attack — it is the payload delivered after an attacker has already gained access. The Sophos 2025 data is definitive: unpatched software and reused or stolen credentials remain the two most common doors left open. Both are preventable with consistent patch management and multi-factor authentication — controls that cost far less than a single incident.
Ransomware initial access vectors (Sophos State of Ransomware 2025)
Source: Sophos State of Ransomware 2025 (3,400 organizations, 17 countries)
| Metric | Value | Source |
|---|---|---|
| Most common entry point: exploited vulnerabilities | 32% of attacks | Sophos State of Ransomware, 2025 |
| Compromised credentials as entry point | 23% | Sophos State of Ransomware, 2025 |
| Phishing as initial ransomware vector | 18% | Sophos State of Ransomware, 2025 |
| Attacks involving data exfiltration before/instead of encryption | ~75% of 2025 cases | Healthcare Ransomware Report, 2025 |
| Organizations stopping attack before encryption (2025) | 44% — six-year high | Sophos State of Ransomware, 2025 |
| Data encryption rate (lowest in six years) | 50% of attacks encrypted data | Sophos State of Ransomware, 2025 |
| Backup use to restore data (lowest in six years) | 54% of victims used backups | Sophos State of Ransomware, 2025 |
Sophos State of Ransomware 2025 →
Key insight: 75% of 2025 ransomware attacks involved data exfiltration before encryption — meaning a solid backup strategy alone no longer prevents the worst outcome. The data is gone even if systems are restored. Defense requires both backup capability and breach prevention.
4 Ransomware by Industry
Attack targeting is not random. Ransomware groups select victims based on three factors: perceived ability to pay, sensitivity of data, and operational dependency on uptime — the more a shutdown hurts, the more leverage attackers have. Manufacturing tops the volume charts because production lines create immediate downtime pressure. Healthcare pays the most per incident because of patient data sensitivity and regulatory exposure. No sector is immune, and the industries CNiC’s clients operate in — professional services, healthcare, finance, legal, and construction — consistently appear in the top-10 target lists.
| Industry | Ransomware Stat | Source |
|---|---|---|
| Manufacturing | #1 by attack volume — 14% of all ransomware incidents; avg demand $1.2M (down 20% from 2024) | Check Point 2026; Sophos Manufacturing Report 2025 |
| Healthcare | 460 federal incidents in 2025; avg breach cost $7.42M; 134 confirmed hospital attacks | HHS / Accountable HQ, 2025; IBM 2025 |
| Government & public sector | 65% increase in H1 2025 YoY; 208 attacks; avg ransom demand $2.3M | Comparitech, 2025 |
| Education (K-12) | 66% of K-12 districts have no specialist cybersecurity staff; avg breach cost $3.80M | BlueVoyant / IBM 2025 |
| Finance & banking | ~$2.06 billion in ransomware losses; avg ransom payment ~$923K | Varonis / Comparitech, 2025 |
| Critical infrastructure | 28% of all ransomware attacks targeted critical infrastructure | Verizon DBIR, 2025 |
Check Point Cyber Security Report 2026 →
See How Managed IT Protects Your Sector →
5 Recovery, Resilience & Defense
The most meaningful shift in the 2025 ransomware data is on the recovery side. Organizations are getting faster at detecting, stopping, and recovering from ransomware attacks — but the improvement is not evenly distributed. Companies with tested incident response plans, validated backups, and proactive monitoring consistently perform better across every metric. The 44% of organizations that stopped attacks before encryption in 2025 did not do so by luck — they had monitoring tools that caught anomalous behavior before file encryption began.
| Recovery Metric | 2025 | 2024 |
|---|---|---|
| Recovered within 1 week | 53% | 35% |
| Took more than 1 month | 18% | 34% |
| Average recovery cost (excl. ransom) | $1.53M | $2.73M |
| Attacks stopped before encryption | 44% (six-year high) | lower |
| Data encryption rate | 50% (six-year low) | 66% |
| Used backups to restore data | 54% (six-year low) | higher |
| Organizations refusing to pay | 64% | 59% |
Sophos State of Ransomware 2025 (Full Report) →
Why backup use dropped to a six-year low: 75% of attacks now involve data exfiltration before encryption, making backup restoration insufficient to resolve the breach. Organizations are increasingly discovering that backups alone are not a complete ransomware strategy — breach prevention must run in parallel.
Ransomware by the Numbers: Summary
| Metric | Value | Source |
|---|---|---|
| Global attack increase (2025 vs. 2024) | 58% | HIPAA Journal / GRIT, 2025 |
| Ransomware in all confirmed breaches | 44% | Verizon DBIR, 2025 |
| Ransomware in SMB breaches | 88% | Verizon DBIR, 2025 |
| Ransomware in large-org breaches | 39% | Verizon DBIR, 2025 |
| Estimated attack frequency | Every ~19 seconds | Total Assure, 2025 |
| US share of global attacks | 55% | GRIT, 2025 |
| Most targeted sector (volume) | Manufacturing (14%) | Check Point, 2026 |
| Most expensive sector (breach cost) | Healthcare ($7.42M avg) | IBM, 2025 |
| Median ransom payment | $115,000 | Verizon DBIR, 2025 |
| Mean ransom payment | $1 million (down 50%) | Sophos, 2025 |
| Median ransom demand | $1.32 million | Sophos, 2025 |
| Total avg ransomware incident cost | $5.08 million | IBM, 2025 |
| Avg recovery cost (excl. ransom) | $1.53 million | Sophos, 2025 |
| SMB recovery cost (100–250 employees) | $638,536 | Sophos, 2025 |
| Victims refusing to pay | 64% | Verizon DBIR, 2025 |
| Paid but failed to fully recover data | 84% | Halcyon Research, Q4 2024 |
| Most common entry point | Exploited vulnerabilities (32%) | Sophos, 2025 |
| Recovered within 1 week | 53% | Sophos, 2025 |
| Attacks stopped before encryption | 44% (six-year high) | Sophos, 2025 |
| Attacks not reported to law enforcement | ~85% | BlackFog, 2025 |
Frequently Asked Questions
How common are ransomware attacks in 2026?
Ransomware was present in 44% of all confirmed data breaches in 2025, up from 32% the year before, according to the Verizon 2025 DBIR. Globally, attacks increased 58% year-over-year. An estimated attack occurs somewhere in the world every 19 seconds, and 85% of incidents are never reported to law enforcement — meaning all published figures represent a fraction of actual activity.
What is the average ransomware payment in 2025?
It depends on the data source. The Verizon DBIR 2025 tracks a median payment of $115,000 across a broad incident dataset. Sophos, which surveys only organizations that experienced ransomware attacks, found the mean payment was $1 million — down 50% from $2 million in 2024. The median ransom demand was $1.32 million, but 53% of paying organizations successfully negotiated the amount down.
Should a business pay a ransomware demand?
Most cybersecurity authorities, including the FBI, advise against paying. The data supports this: 84% of organizations that paid in Q4 2024 still failed to fully recover all their data (Halcyon Research). Paying also funds future attacks and may create legal exposure if the attacker group is under OFAC sanctions. In 2025, 64% of victim organizations refused to pay — up from 50% two years prior — reflecting improved backup and recovery capabilities.
Which industries are most targeted by ransomware?
Manufacturing leads by attack volume at 14% of global incidents in 2025, followed by technology (9%) and retail/wholesale (7%). Healthcare ranks highest by cost at $7.42 million per breach and experienced 460 federal incidents in 2025 alone. Government and public sector saw a 65% increase in attacks in the first half of 2025. Every sector is a target — attackers select victims based on ability to pay, data sensitivity, and operational dependency on uptime.
How long does recovery from a ransomware attack take?
Recovery times improved significantly in 2025. According to Sophos State of Ransomware 2025, 53% of organizations fully recovered within one week — up from 35% in 2024. Only 18% took more than a month, down from 34% in 2024. The key differentiators are tested backup plans, pre-defined incident response roles, and active monitoring that detects attacks before encryption completes. Average recovery cost excluding the ransom fell 44% to $1.53 million.
Methodology & Sources
All statistics are traced to primary or verified Tier 2 sources. We do not cite aggregator blogs quoting other blogs. Where multiple sources report different figures for the same metric, both are presented with scope clearly distinguished.
Primary sources used
- Verizon 2025 Data Breach Investigations Report (DBIR) — 22,000+ incidents, 12,195 confirmed breaches. verizon.com →
- Sophos State of Ransomware 2025 — 3,400 IT/cybersecurity leaders, 17 countries, vendor-agnostic. sophos.com →
- IBM Cost of a Data Breach Report 2025 — 600 organizations, 17 industries, Ponemon Institute. ibm.com →
- FBI Internet Crime Complaint Center (IC3) 2025 Annual Report. fbi.gov →
- Check Point Cyber Security Report 2026. checkpoint.com →
- HIPAA Journal Ransomware Report 2025. hipaajournal.com →
- Halcyon Ransomware Research Q4 2024 — ransom payment outcome data.
- BlackFog Ransomware Report 2025 — unreported attack rate data.
- Comparitech Ransomware Roundup 2025 — sector-specific attack counts.
Last updated: May 2026. Update schedule: Updated quarterly as primary reports are released.
Payment figure note: Verizon DBIR and Sophos report different median payment figures because they measure different populations. Verizon’s $115,000 reflects a broader incident dataset; Sophos’s $1 million reflects organizations that confirmed ransomware contact and payment. Both figures are accurate for their respective contexts.
related posts
Ransomware Payout Statistics 2026: What Victims Actually Pay
May 15, 2026Ransomware payments tell a story of contradictions. In 2024, total global ransom payments dropped 35% year-over-year…
Small Business Cyber Attack Statistics (2026): Attack Rates, Costs, and Defense
May 14, 2026Small and medium businesses experienced approximately 4 times more confirmed data breaches than large organizations in…
Average Cost of a Data Breach Statistics (2026): By Industry, Country &…
May 14, 2026The average data breach now costs US organizations $10.22 million — an all-time high for any…
Cybersecurity Statistics (2026): 52+ Data Points on Cybercrime
May 14, 2026US cybercrime losses hit $20.9 billion in 2025 — a 26% jump year-over-year and the first…